The techniques malware writers use nowadays are becoming more and more sophisticated. The last time I spotted a malware was almost two years ago. At that time, a page that I was visiting contained a JPEG image that was exploit by a zero-day vulnerability.
This time however, I stumbled upon a malware that uses code injection to insert an iframe into a webpage and when the webpage is visited, a page that disguised as some sort of antivirus software would pop up. If the user was successfully tricked into thinking that his or her antivirus software was running and clicked the confirmation button by mistake the result would be disastrous.
It seems that the malware first try to inject the script located at the url below into a webpage (WARNING! DO NOT GO TO THE FOLLOWING URLs, OTHERWISE YOUR COMPUTER MIGHT BE INFECTED):
http://batalion.cc/hail/
and if the page does not handle user inputs correctly (I.e. does not escape the input), the script would be executed when the page is viewed.
The script itself eventually opens an iframe targeted at the following url:
http://scan.antivirus2008scanner.com/100655/3/
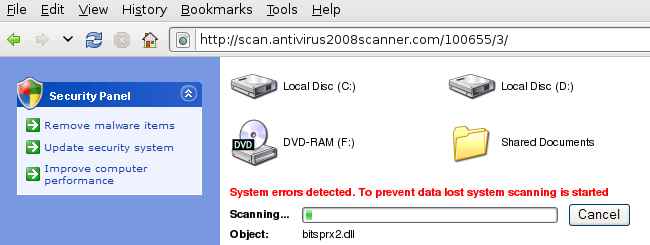
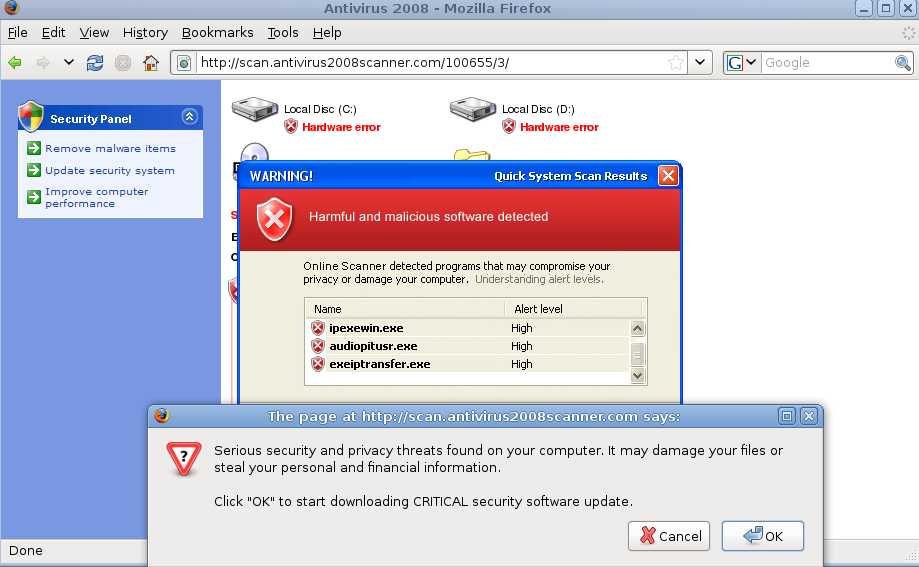
This code shows an animated image mimicking a typical antivirus software (see images below):
After the animation, it will “report” that it “found virus” and ask the user whether he or she wants to remove it. If the user is not careful, and clicked the “remove” button: the following code will be downloaded:
http://dwl.av2008dl.com/load/setup_100655_3_.exe
And if that executable is run, the machine will be infected.
The above exploit seems to work with the default FireFox settings (javascript enabled), and it is likely exploitable in IE.
This kind of exploits are particularly dangerous as any browser that supports iframe and javascript could be targeted, and most users do not have javascript turned off by default (web 2.0 makes it almost impossible to live without javascript engine). Of course, this particular exploit only works on Windows. So you should be safe if you are running Linux with the least privileges…